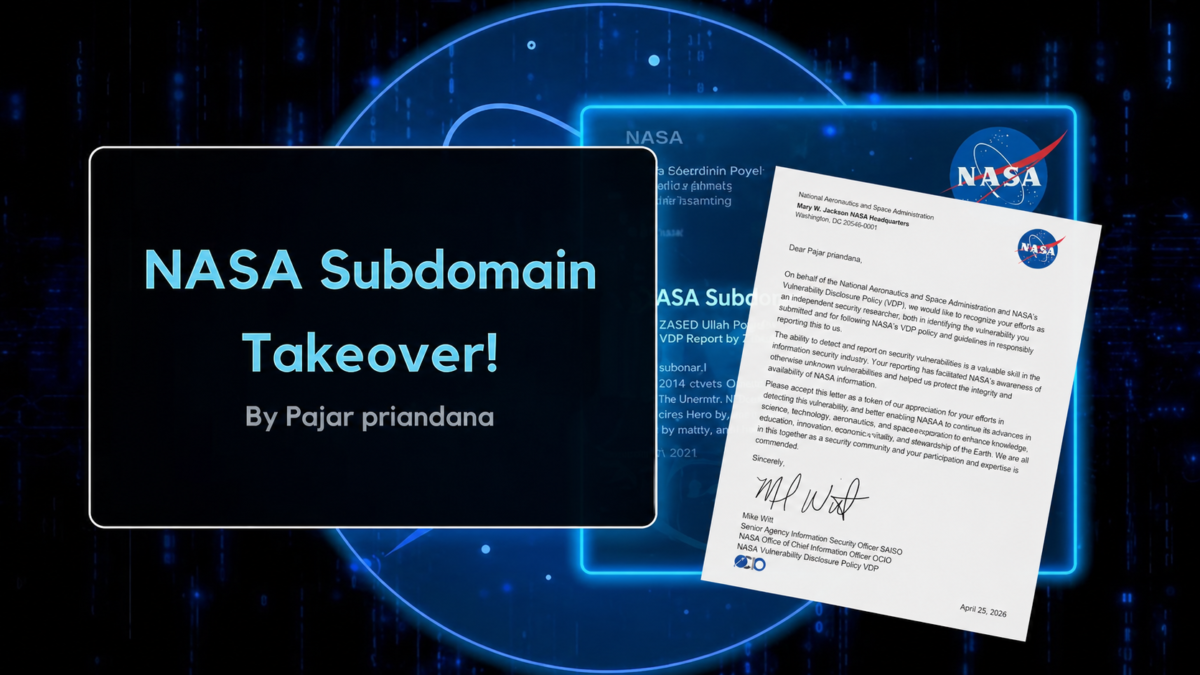
Researcher: Pajar Priandana
Program: NASA – Vulnerability Disclosure Program (VDP)
Status: Resolved
Severity: P3 (Subdomain Takeover)
Category: Misconfigured DNS
Introduction
During routine reconnaissance under the NASA Vulnerability Disclosure Program (VDP), I identified a GitHub Pages subdomain takeover affecting:
xxx.nasa.gov
The subdomain was pointing to GitHub Pages infrastructure, but no corresponding repository was configured — leaving it unclaimed.
This created a high-risk scenario where an attacker could host arbitrary content under a trusted government domain.
🔍 Recon & Identification
Step 1 — DNS Check
A DNS lookup showed the subdomain resolves to GitHub Pages:
dig xxx.nasa.gov +short
xxx.xxx.xxx.xxx
xxx.xxx.xxx.xxx
xxx.xxx.xxx.xxx
xxx.xxx.xxx.xxx
Step 2 — Subdomain Access
Accessing:
https://xxx.nasa.gov

Returned a GitHub 404 page, indicating:
✔ DNS points to GitHub
✘ No repository configured
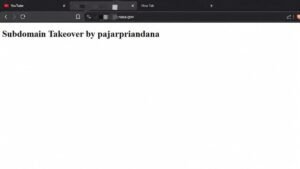
🧪 Exploitation (Ethical PoC)
Using GitHub Pages, I configured:
xxx.nasa.gov

Then deployed:
<h1>Subdomain Takeover by pajarpriandana</h1>
Result:
Subdomain successfully taken over (PoC only, non-harmful).
🛠️ Remediation
The NASA team resolved the issue by:
✔ Removing DNS records
✔ Cleaning unused GitHub mappings
Status: Resolved
🏆 Recognition
Severity: P3
Category: Misconfigured DNS
Program: NASA VDP
Appreciation: Letter of Appreciation (LoA)
🔚 Note

Some technical details have been intentionally redacted for responsible disclosure.







